Know-how reporters
 Getty Photos
Getty PhotosThe UK has uncovered what it says is a “malicious cyber marketing campaign” concentrating on a number of organisations, together with these concerned in delivering international help to Ukraine
After a joint investigation with allies together with the US, Germany and France, the UK’s Nationwide Cyber Safety Centre (NCSC) mentioned a Russian navy unit had been concentrating on each private and non-private organisations since 2022.
These embody organisations concerned in supplying defence, IT providers and logistics assist.
The safety our bodies of 10 Nato nations and Australia mentioned Russian spies had used a mixture of hacking methods to realize entry to networks.
A number of the targets have been internet-connected cameras at Ukrainian borders which monitored assist shipments going into the nation.
The report additionally says a tough estimate of 10,000 cameras have been accessed close to “navy installations, and rail stations, to trace the motion of supplies into Ukraine.
It provides the “actors additionally used official municipal providers, resembling site visitors cams.”
The Russian navy unit blamed for the espionage known as GRU Unit 26165 however goes by quite a few casual names, together with Fancy Bear.
The infamous hacking crew is understood to have previously leaked World Anti-Doping Company knowledge, and performed a key position in the 2016 cyber-attack on the US’s Democratic Nationwide Committee, in keeping with safety specialists.
“This malicious marketing campaign by Russia’s navy intelligence service presents a critical threat to focused organisations, together with these concerned within the supply of help to Ukraine,” Paul Chichester, NCSC Director of Operations, mentioned in a press release.
“We strongly encourage organisations to familiarise themselves with the menace and mitigation recommendation included within the advisory to assist defend their networks,” he added.
Anybody concerned in transferring items into Ukraine “ought to take into account themselves focused” by Russian navy intelligence, John Hultquist, chief analyst at Google Menace Intelligence Group, mentioned.
“Past the curiosity in figuring out assist to the battlefield, there may be an curiosity in disrupting that assist by both bodily or cyber means,” he mentioned.
“These incidents could possibly be precursors to different critical actions.”
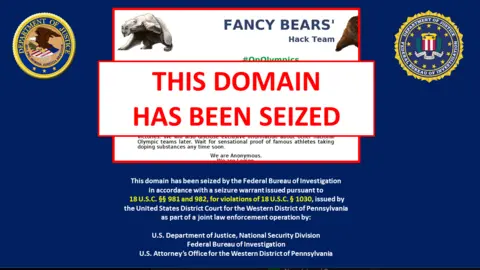 Web Archive
Web ArchiveThe joint cyber-security advisory mentioned Fancy Bear had focused organisations linked to crucial infrastructure together with ports, airports, air site visitors administration and the defence business.
These have been in 12 mainland European nations and the US.
The hackers used a mixture of methods to realize entry, the report mentioned, together with guessing passwords.
One other technique used known as spearphishing, the place faux emails are focused at particular individuals who have entry to techniques.
They’re introduced with a faux web page the place they enter their login particulars, or inspired to click on a hyperlink which then installs malicious software program.
“The themes of spearphishing emails have been various and ranged from skilled matters to grownup themes,” the report mentioned.
A vulnerability in Microsoft Outlook was additionally exploited to gather credentials “by way of specifically crafted Outlook calendar appointment invites”.
These sorts of methods have been “a staple tactic of this group for over a decade,” Rafe Pilling, director of menace intelligence at Sophos Counter Menace Unit, mentioned.
Digital camera entry “would help within the understanding of what items have been being transported, when, in what volumes and assist kinetic [weapons] concentrating on,” he added.
Cyber safety agency Dragos instructed the BBC it had been monitoring hacking exercise linked to that reported by the NCSC.
It is chief govt Robert M. Lee mentioned that the hackers it adopted weren’t solely fascinated with gaining a foothold in company laptop networks however would infiltrate industrial management techniques the place they might be capable to “steal vital mental property and insights for espionage, or place themselves for disruptive assaults”.